EDR Silencers and Beyond: Exploring Methods to Block EDR Communication - Part 1
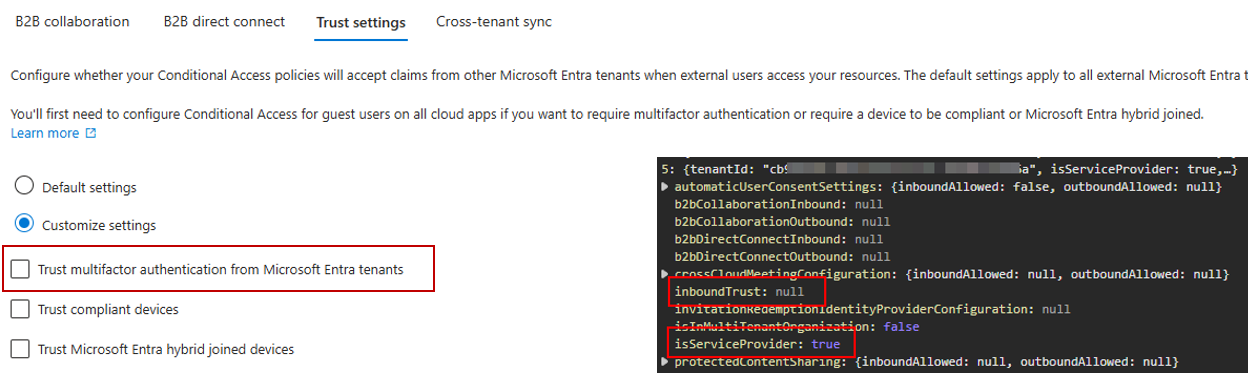
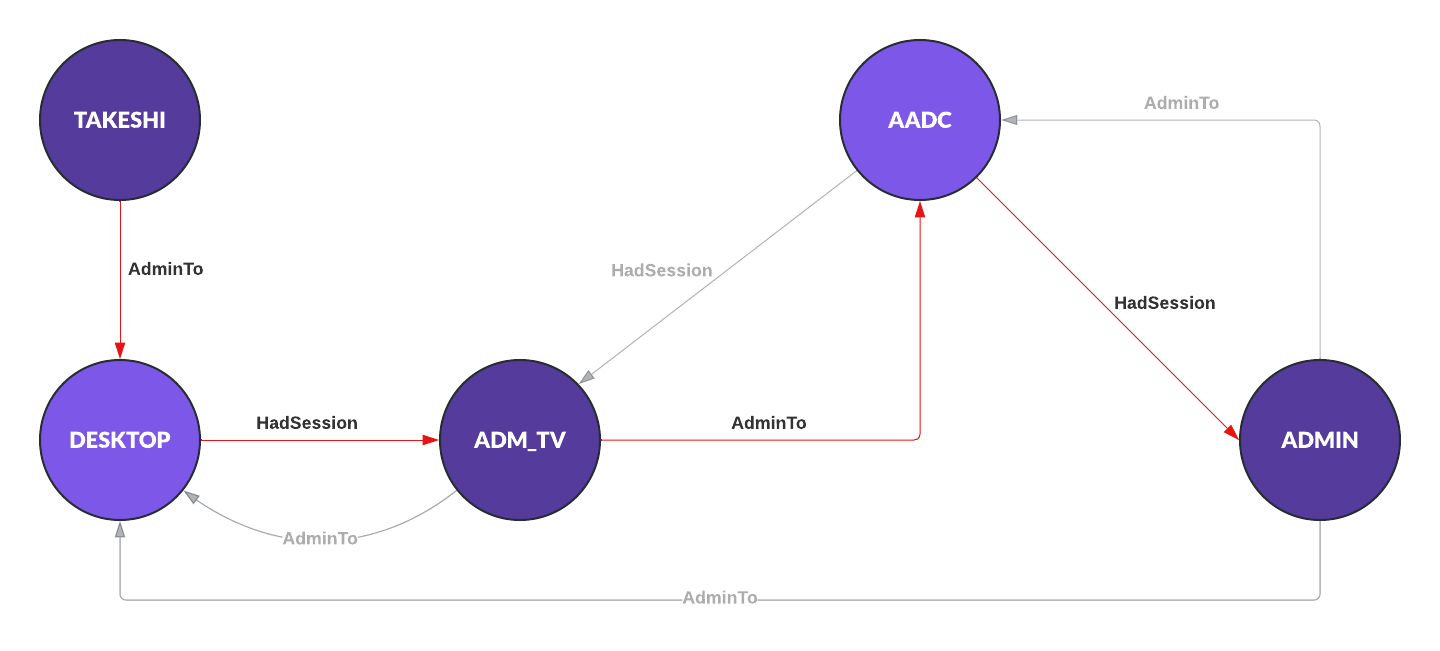
For red teams and adversary alike it’s important to stay hidden. As many companies nowadays have EDR agents deployed those agents are always in focus and tools like EDRSilencer or EDRSandblast use different techniques to prevent further communications of the EDR agent with the log ingestion endpoint.
A few weeks ago Mehmet Ergene and I were discussing other ways to prevent agent communications and ways to detect such tampering. The idea for a a two part blog post was born. While I cover only one “novel” way to block EDR Mehmet has released part 2 which covers other angels.