SCHANNEL settings in Azure Windows Marketplace image changed
A couple of weeks ago I recognized new registry keys the SCHANNEL settings of the Windows 2016 Azure Marketplace image. Those setting are different from a manually deployed and updated Windows machine!
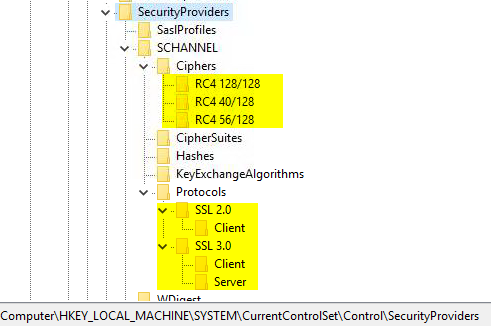
The newly created registry keys disable the following ciphers and protocols
- Ciphers
- RC4 128/128
- RC4 40/128
- RC4 56/128
- Protocols
- SSL 2.0 Client
- SSL 3.0 Client/Server
First of all: The settings changed are regarding old ciphers and protocols that should be disabled in any secure environment after all! Some of them are even disabled without any registry keys starting Windows 2016 already.
Microsoft has published an article “TLS (Schannel SSP) changes in Windows 10 and Windows Server 2016” which describes the changes made in those OS version for release. This includes the deactivation of NULL, MD5, DES, and export ciphers.
Also it states that SSL 2.0 has been removed completely, and SSL 3.0 client and server is disabled by default. This makes the registry changes obsolete and only configures the defaults in place.Maybe Microsoft did this to help some poorly configured audit tool to show successful results or to better show the default config to the administrator.
In 2013 Microsoft published the “Security Advisory 2868725” which states the mentioned RC4 ciphers should be disabled. So after about 5 - 6 years later Microsoft has implemented this best practice for all newly deployed Azure VMs. Sadly it did not document the change anywhere.
Please be aware that if you deploy a Windows 2016 server from ISO and install the latest updates RC4 will still be active with the exception when using SCH_USE_STRONG_CRYPTO, as you can read here.