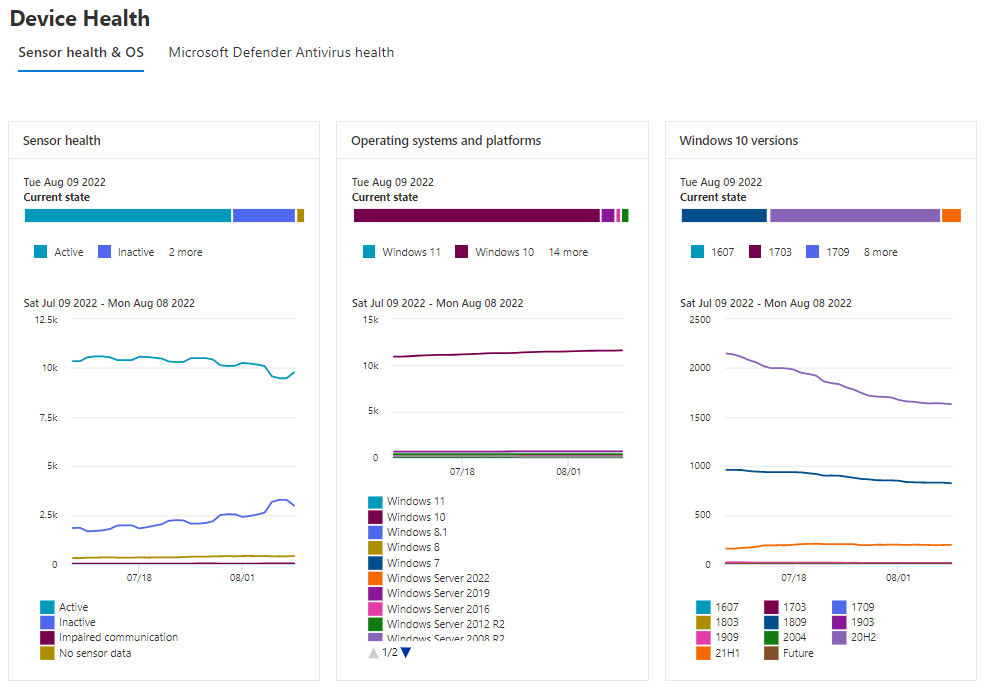
Microsoft Defender for Endpoint Device Health
Microsoft just announced the public preview of the new Device Health Reporting for Microsoft Defender for Endpoint and I already love it. It not only gives you deeper insights into your environment but also adds much needed information like engine version, last scan time, and scan results.