On Thursday, April 28th, I will be speaking at the Microsoft Cloud Security User Group virtual meetup. The topic of my talk is “Use external threat intelligence in Microsoft Defender for Endpoint”.
Abstract Extend alarming and protection capabilities of Microsoft Defender for Endpoint using external data sources. In this showcase Fabian Bader will demonstrate how easy you can tap into open source threat intelligence using the Feodo Tracker project and use it to protect your endpoints.
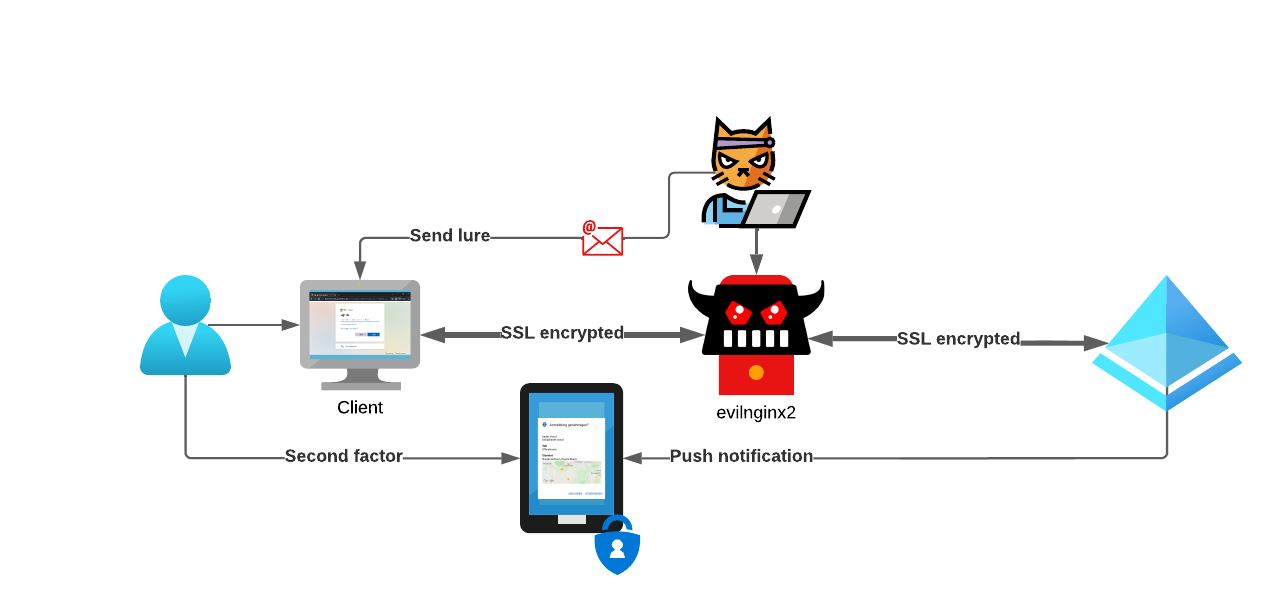
Microsoft offers a great variety of options to use as your primary authentication method, when signing-in with your Entra ID (Azure AD) identity using a browser.
Username and Password Phonenumber and SMS Username and Passwordless phone sign-in Certificate-based authentication Windows Hello for Business FIDO2 security keys Using conditional access you can further protect the accounts, enforcing the need for a second factor, device compliance, location based restrictions and many more configuration options.
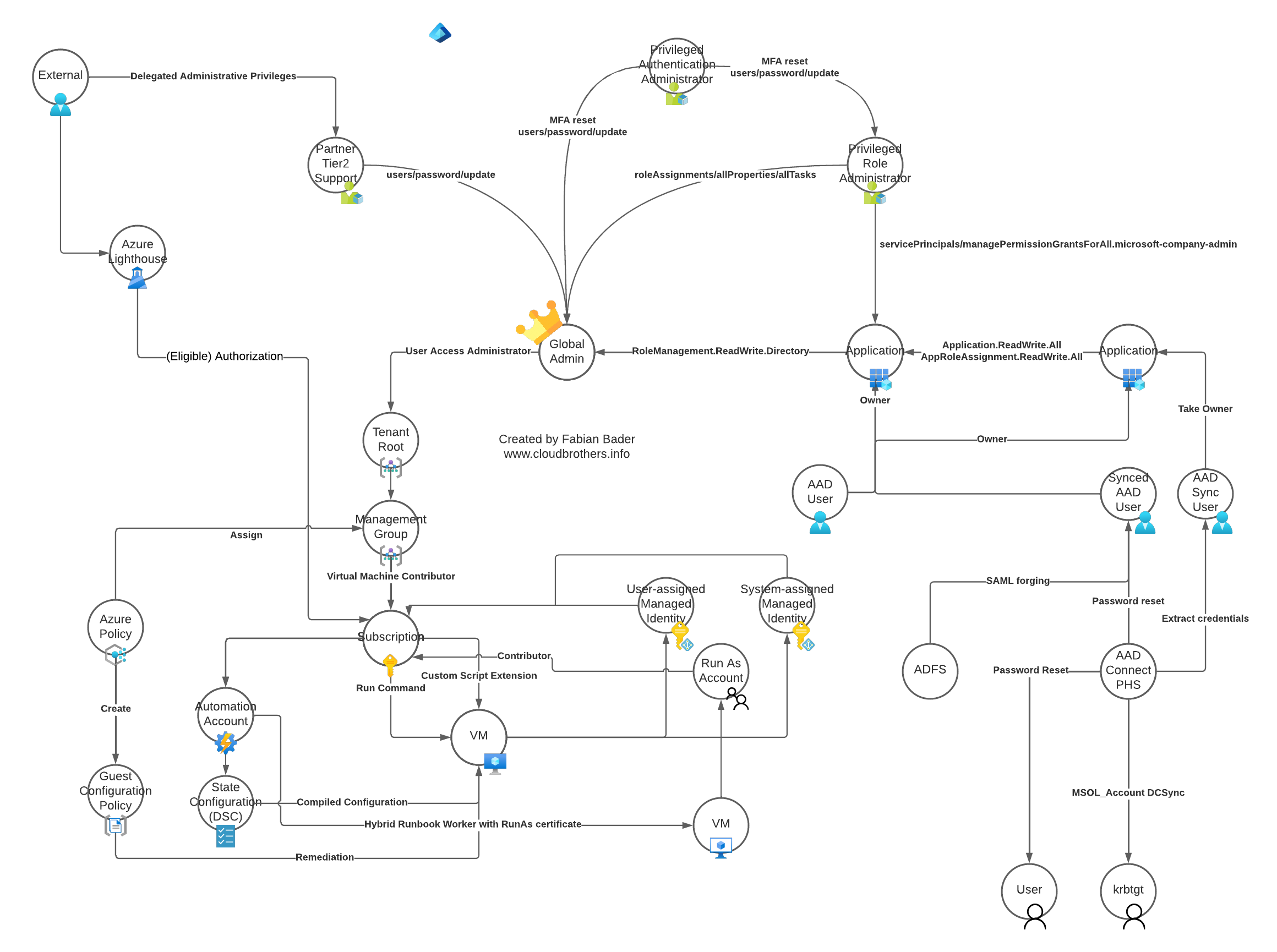
Creating and maintaining a secure environment is hard. And with every technology or product added to your environment it gets more complicated. Microsoft Azure as a cloud environment is no exception to this rule and with the many services and features that get added every year it just gets more complicated even if you did not change a thing. Because keeping your IT assets secure is important as you move to the cloud, it is important to know which bad practices to avoid and which attack scenarios are out there.
Microsoft does a great job in detecting and preventing malware and phishing emails with Microsoft Defender for Office 365. Since this feature works mostly in the background, even larger than usual malware campaigns are prevented without the Administrator noticing.
Campaign view Using the campaign view you can check for those events and get a good overview which kind of malware is targeting your users.
Campaign overview You can also drill down even further to identify which users were targeted as part of this campaign.
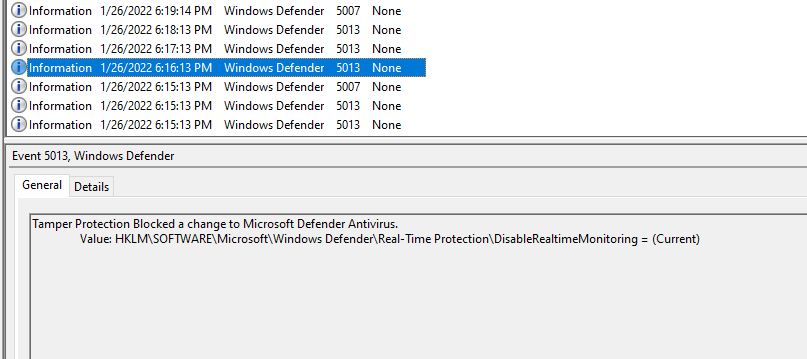
Intro In this article I explore the limits of the Microsoft Defender Antivirus (MDAV) Tamper Protection feature using only native configuration changes using mechanisms available to any user with administrative permissions. So I will not use any AV bypasses like sandboxing, token stealing or anything like this.
In addition I also documented the built-in detection capabilities of Microsoft Defender for Endpoint to show you, what alerts you can expect in your environment.
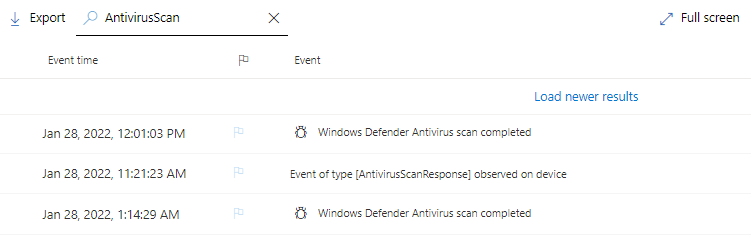
Microsoft Defender for Endpoint has great automation capabilities and you can alert using custom detection rules. Put that together and you can trigger many on-client events using those custom detection. This could be to isolate the device from the network, start an automated investigation, collect an investigation package, restrict app execution or run an full antivirus scan on the device in question.
But how do you know if Microsoft Defender Antivirus has finished to scan the device?