Journey To Passwordless: FIDO2

Blog series
- Passwordless: But why?
- Enable passwordless
- Temporary Access Pass
- FIDO2 Security keys
- Windows 10 device onboarding and Windows Hello for Business
- PowerShell administration without a password
- Microsoft Authenticator app
- Restrict FIDO2 key usage & conclusion
Recap
Last week I explained the initial setup of an admin account using Temporary Access Pass. Today I want to introduce FIDO2, a sign-in method intended for regular sign-ins.
What is FIDO2?
FIDO is short for Fast Identity Online and FIDO2 is an industry standard of the FIDO Alliance for authentication on the web (WebAuthn). This standard offers a non-phishable way to sign-in to web services without a password. This is also the biggest difference to the first version FIDO U2F, which could only be used as a second factor for the sign-in.
Microsoft supports passwordless sign-in with FIDO2 security keys in Entra ID (Azure AD), but not FIDO U2F keys.
Authentication with a FIDO2 Security Key involves the following steps:
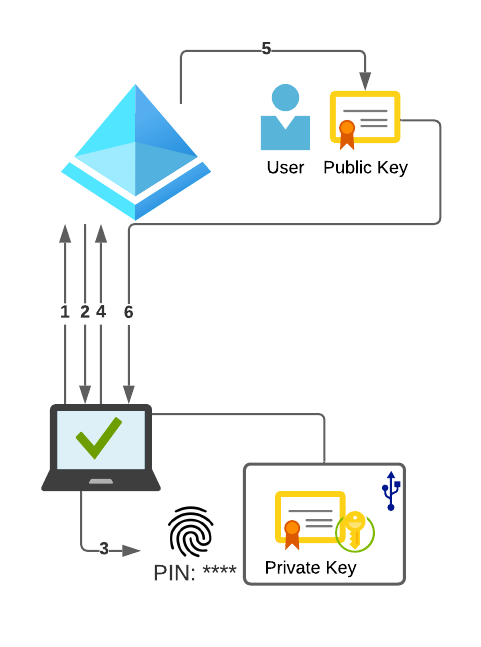
- The authentication provider on the client sends an auth request to the Entra ID (Azure AD) during the login process
- The Entra ID (Azure AD) responds to this request with a random and arbitrary number, the nonce.
- The user unlocks the private key in the FIDO2 secure enclave using a PIN or biometric method (facial recognition or fingerprint) and confirms that he is present by physically touching the key. Now the client signs the received nonce with the private key.
- After the nonce is signed, it is sent back to the Entra ID (Azure AD).
- The Entra ID (Azure AD) verifies the signature with the public part of the key and compares the nonce.
- If the nonce is valid, the Entra ID (Azure AD) responds with a primary refresh token (PRT).
- With this PRT the user can now access services like Mail or Teams.
Technical requirements
The most important requirement is a supported FIDO2 key.
Furthermore, the usage is only possible with a supported browser and operating systems. In short, Chrome and Chromium-based Microsoft Edge are supported on Windows, Linux and macOS.
While USB can be used as a connection method on all operating systems, Bluetooth Low Energy and NFC can only be used on Windows computers.
We have created all other technical prerequisites in Entra ID (Azure AD) in the last two blog entries.
Even though this blog article uses FEITIAN’s FIDO2 keys, all basic functions can be implemented with any Microsoft-certified FIDO2 security key.
PIN vs. biometry

Each time the private key material in FIDO2 is accessed, this access must be approved. This security feature prevents anyone from accessing the data if the key is lost.
This approval is given, for example, by entering a PIN and physically touching the security key. FEITIAN eliminates the need to enter a PIN by cleverly using biometric features in your BioPass FIDO2 keys. The method used in both cases is a fingerprint.
Physically touching the key verifies the user’s fingerprint and, if the fingerprint is correct, releases the private key material for sign-in. The enrollment flow is thus shortened by one step.
As for the security of fingerprint recognition, FEITIAN claims the false accept rate to be 0.001%.
FEITIAN BioPass FIDO2 K27 + K33

The two FIDO2 Security Keys differ mainly in the supported interfaces.
| Interface | K27 | K33 |
|---|---|---|
| USB-A | Yes | No |
| USB-C | No | Yes (female) |
| Bluetooth LE | No | Yes |
| NFC | No | Yes |
| Preis | 60 $ | 90 $ |
While the K27 offers broad support for all kinds of computers via the USB-A port, the K33 can be operated completely wireless. Virtually every modern laptop supports Bluetooth LE. If that is not possible, the key can be connected directly with a USB-C cable.
Inital setup
The first step in setting up FIDO2 Security Keys is to add a fingerprint.
There are two ways to do this on Windows.
- FEITIAN BioPass FIDO2 Manager
- Windows Sign-In options (>= Windows 10 1903)
The BioPass FIDO2 Manager can also be downloaded for Linux and macOS.
BioPass FIDO2 Manager
Both security keys must be connected to the computer via USB for the initial setup.
After starting the BioPass FIDO2 Manager you can add the first fingerprint.
You have the choice between “PIN and fingerprint” or “Fingerprint only”. It is a good idea to use the PIN as a backup option, for example if you have an injured finger.
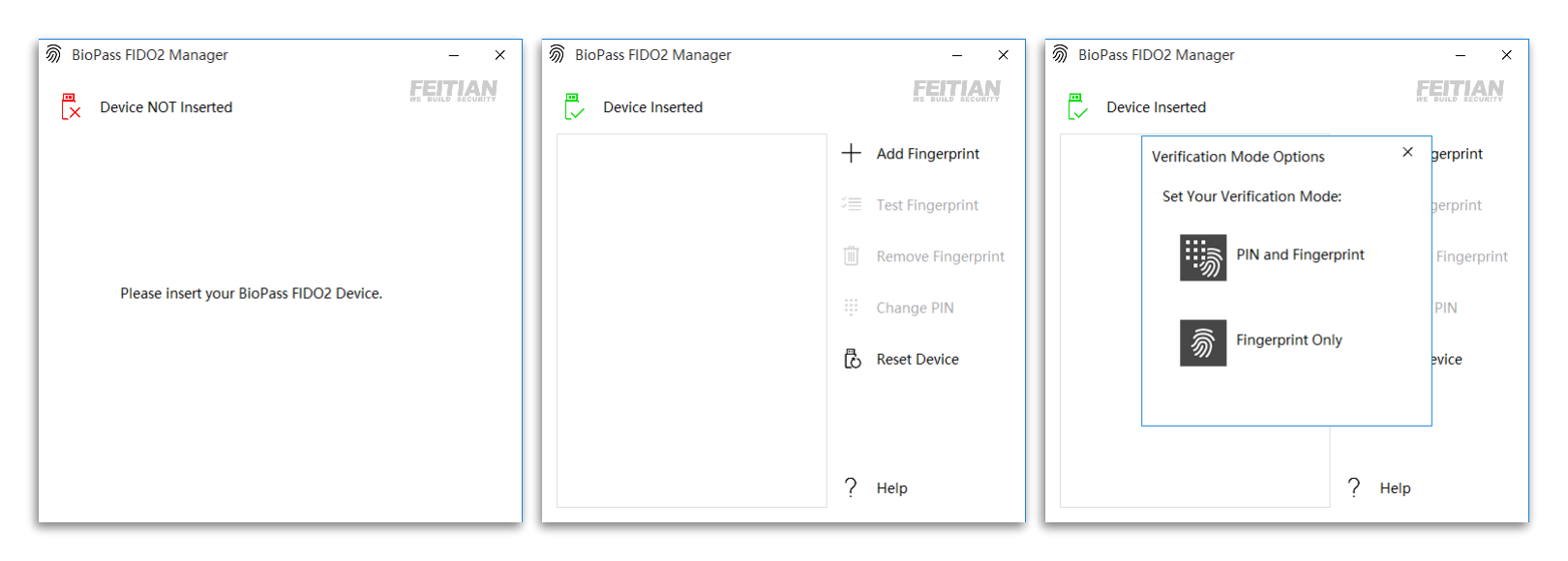
During the initial setup with PIN, the contact sensor of the security key must be touched after entering the PIN and clicking “OK”. The software does not display a prompt to do this, but otherwise runs into an error. This condition is described in the detailed operating instructions.
Each fingerprint that is enrolled must be confirmed four times.
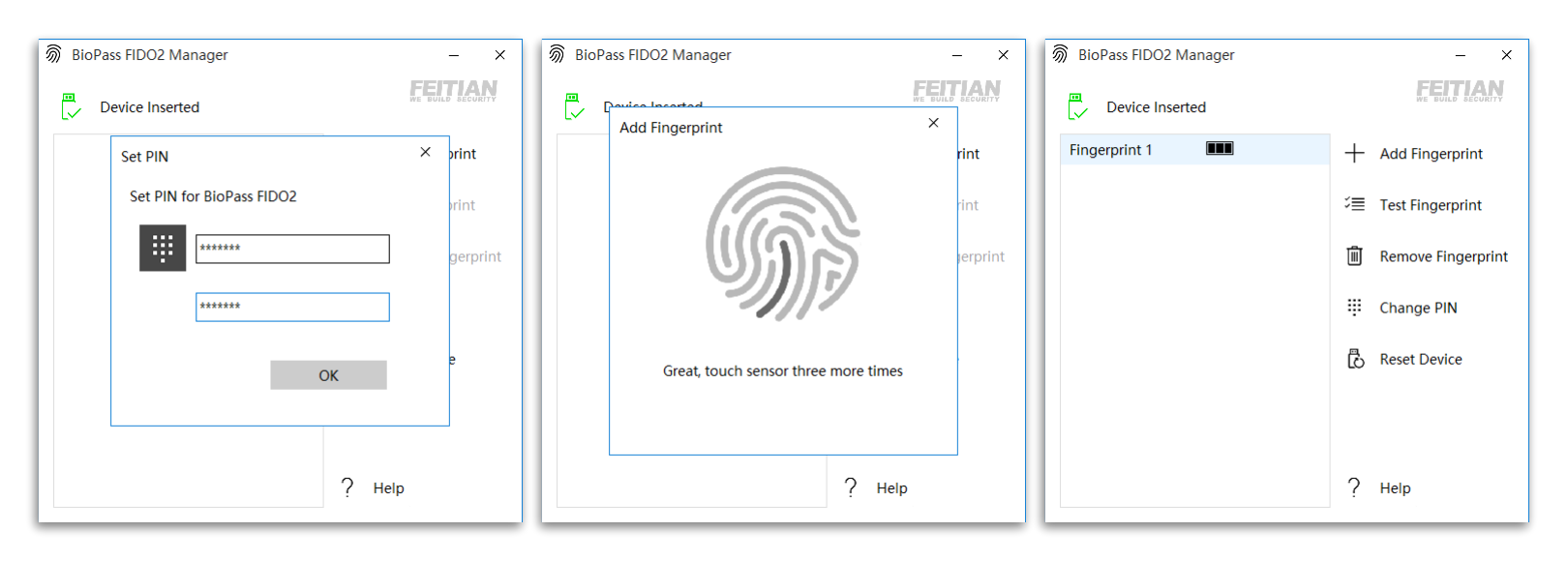
Windows Sign-In options
In Windows 10, the security key can also be set up natively. The only difference is that the option “Fingerprint only” is not available. A PIN must always be set up before the first fingerprint can be registered.
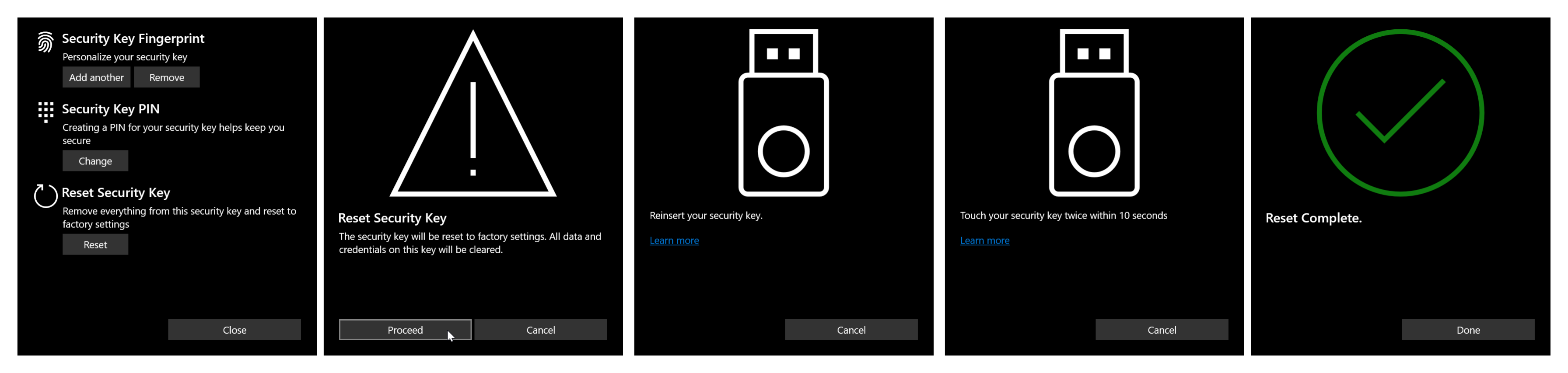
Reset the security key
The security key can only be reset within the first 10 seconds after connection. Confirmation with a valid fingerprint or PIN is not necessary. Since the private key material is completely deleted and the key can no longer be used for sign-in, this is not a security problem.
Connect via Bluetooth
Once the K33 is set up, it can be connected to a computer via Bluetooth.
Open the Bluetooth Settings and search for new Bluetooth devices. Then turn on the K33 and press the On/Off switch for about 5 seconds until the blue Bluetooth LED blinks fast.
In the list of discovered devices you should see a new device named “FT_nnnnn”, where nnnnn is the serial number of the security key.
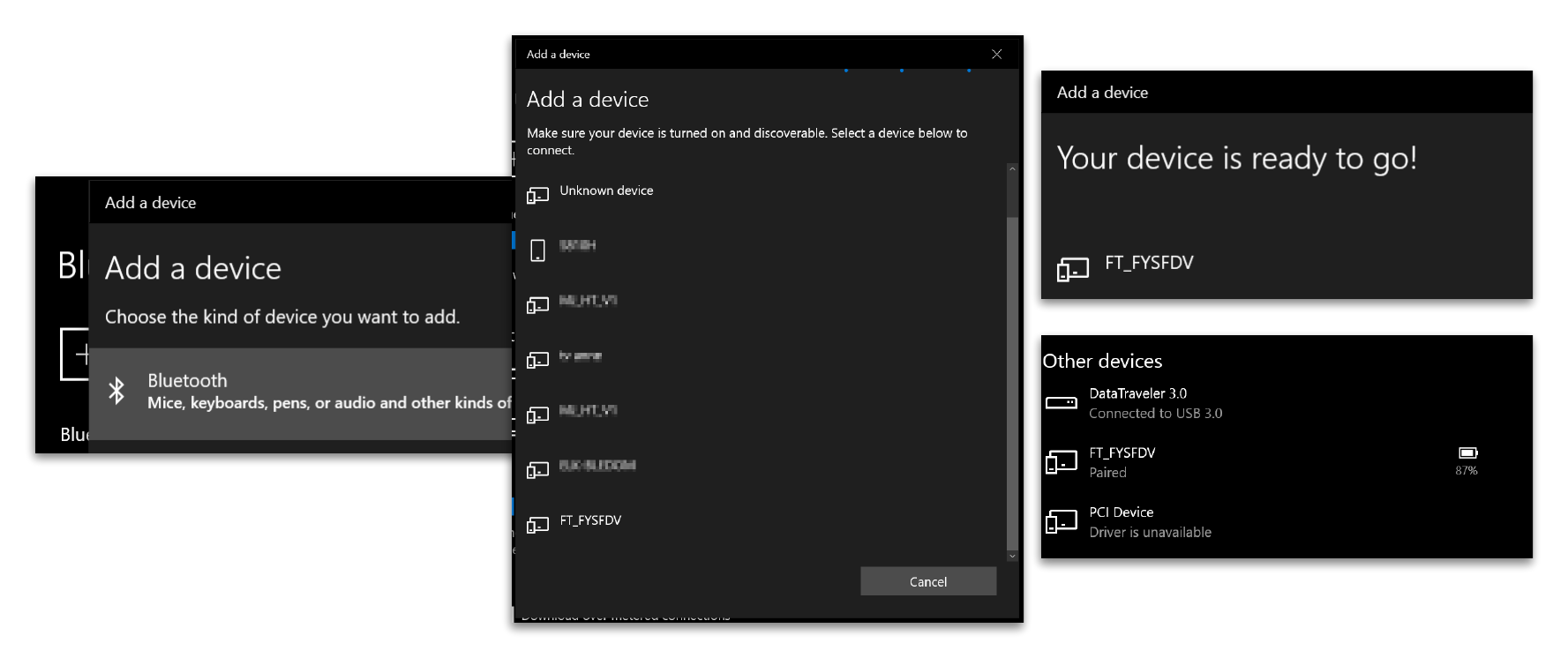
Once the key is successfully connected, it can be used wirelessly.
Add Security Key to AAD User
After sign-in with the Temporary Access Pass, the Security Key must be added as a login method to My Security Information.
In the portal, select “Add method” and then select “Security key” as the method.
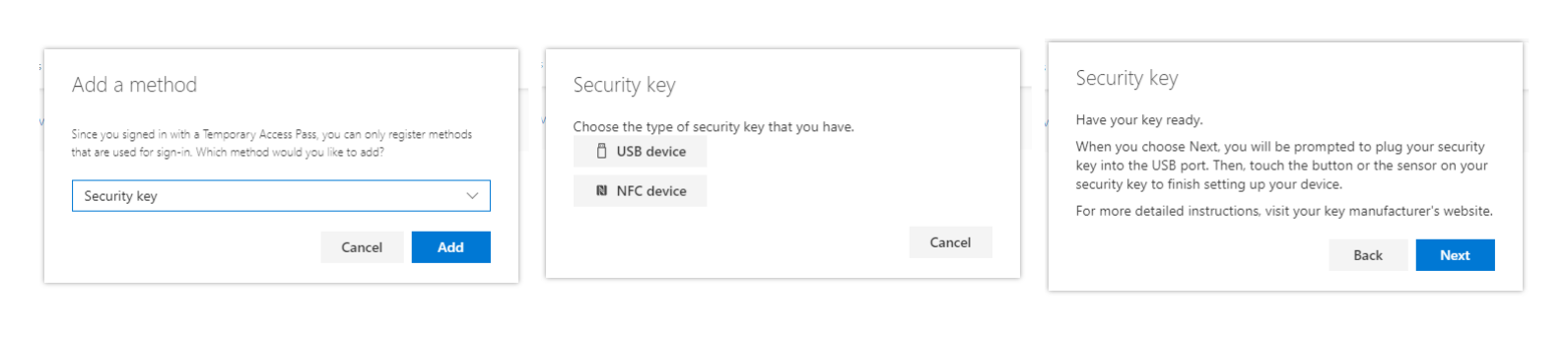
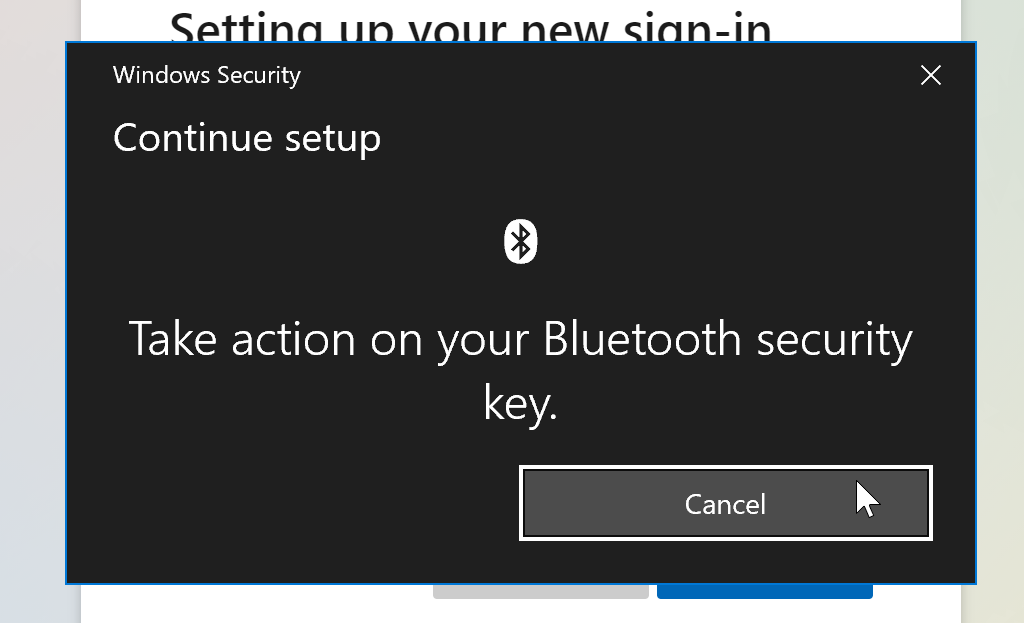
No matter if Bluetooth or USB-A, USB must always be selected as connection type.
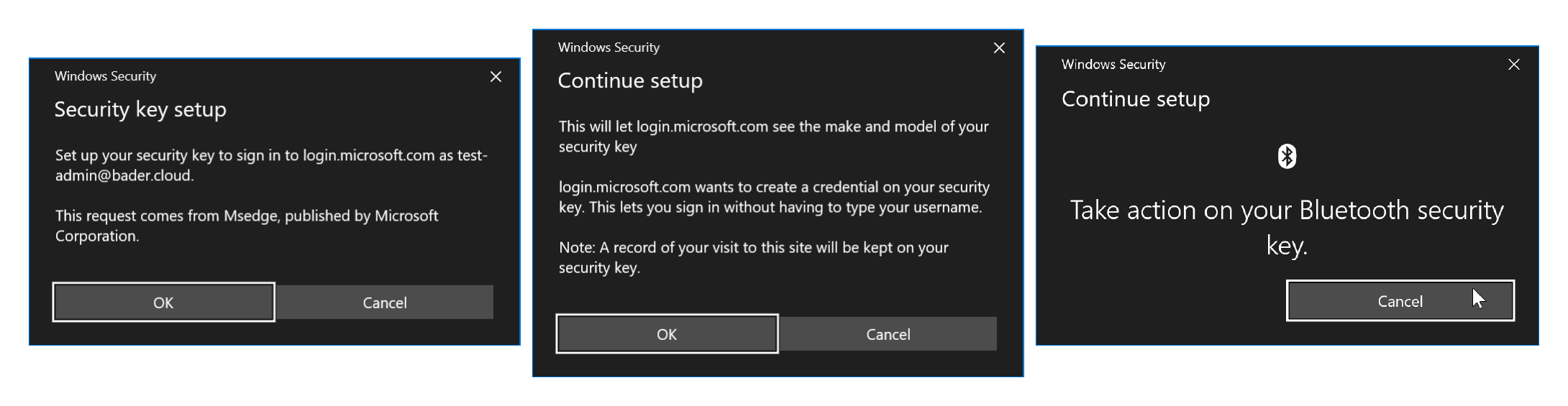
Confirm the request to access the key and unlock the FIDO2 Security using fingerprint.
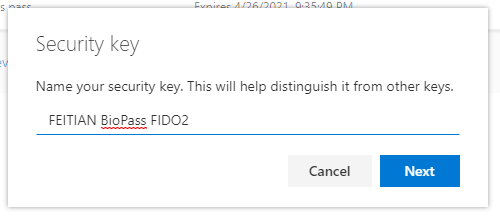
Finally, select a descriptive name for the security key and confirm.
Now you can login with your FIDO2 security key.
Browser-based sign-in using the security key
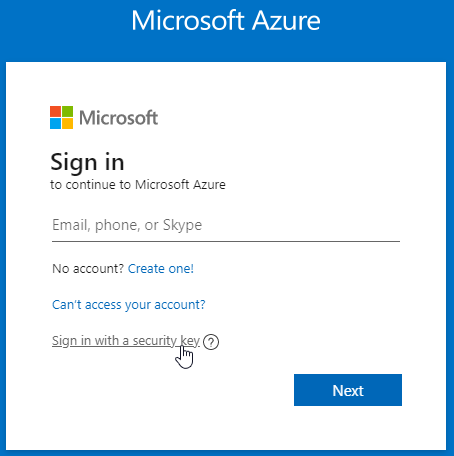
The next time you sign-in to Entra ID (Azure AD) using a browser, you can directly select “Sign in with security key”. You don’t have to enter your user name.
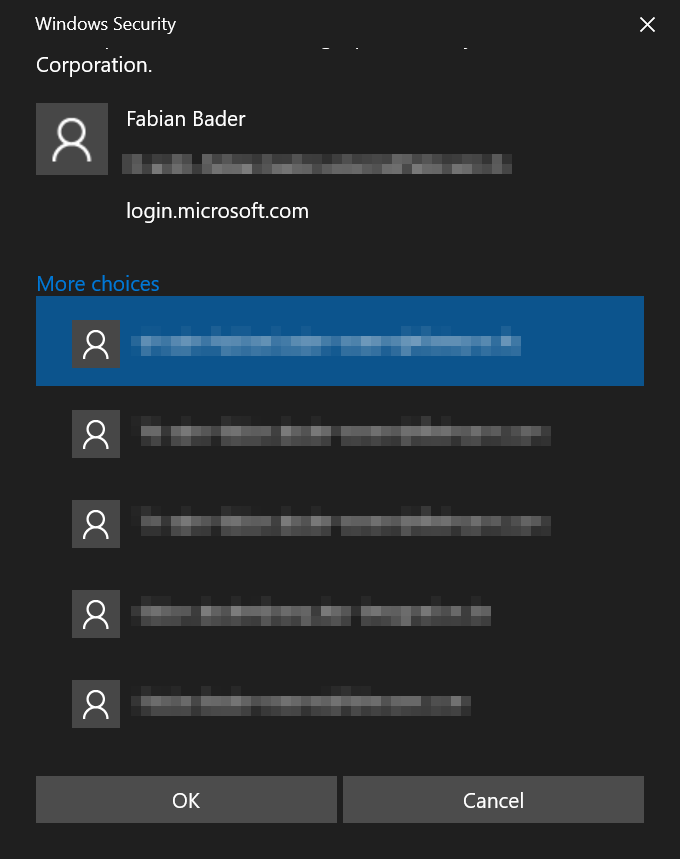
The big advantage of the FIDO2 security keys is that several (up to 128) accounts can be stored on the key. As soon as more than one account is connected to the key, a selection list is displayed during sign-in. This makes this kind of password-less sign-in especially useful for people with many accounts.
Now the security key has to be unlocked for the sign-in, the computer asks you to touch the security key. Since the fingerprint releases the key and thus one touch is sufficient, the sign-in is completed after only a few seconds.
At no time was a password sent over the Internet that could be intercepted and reused.
FEITIAN - Pass to Passwordless
FEITIAN offers, under certain conditions as part of the Path To Passwordless program, a free kit for evaluation.
Next steps
Now that the security key for passwordless sign-in to the browser works, the next step is to set up a Privileged Admin Workstation (PAW). Of course also 100% passwordless.