TIL BitLocker + YubiKey = ❤️
TIL is a blog series in which I document (for me) interesting insights.
This knowledge is possibly already documented a hundred times on the Internet. But so i can find it again i wrote it down here.
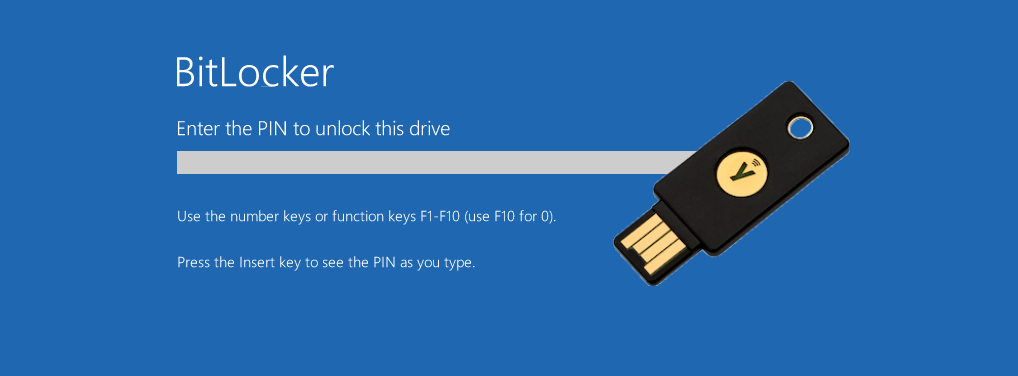
BitLocker provides a convenient way to encrypt the hard drive on computers running Windows 10 Professional.
A YubiKey is my choice for passwordless sign-in to Entra ID (Azure AD).